The AWS Identity and Access Management service is essential to master to manage access control of an AWS account. The service provides the necessary permissions to allow or deny service actions, such as uploading an object to an S3 bucket or launching an EC2 instance, to a principal (an entity that performs actions).
Within an organization’s AWS account, users and groups are created to represent the entities that perform the actions. In cases a 3rd party like a consulting partner need to access the AWS account, roles provide a secured and controlled way of accessing your AWS resources.
This article shows the steps to create a role that allows a 3rd party to access your AWS account.
Setup the AWS Account Alias
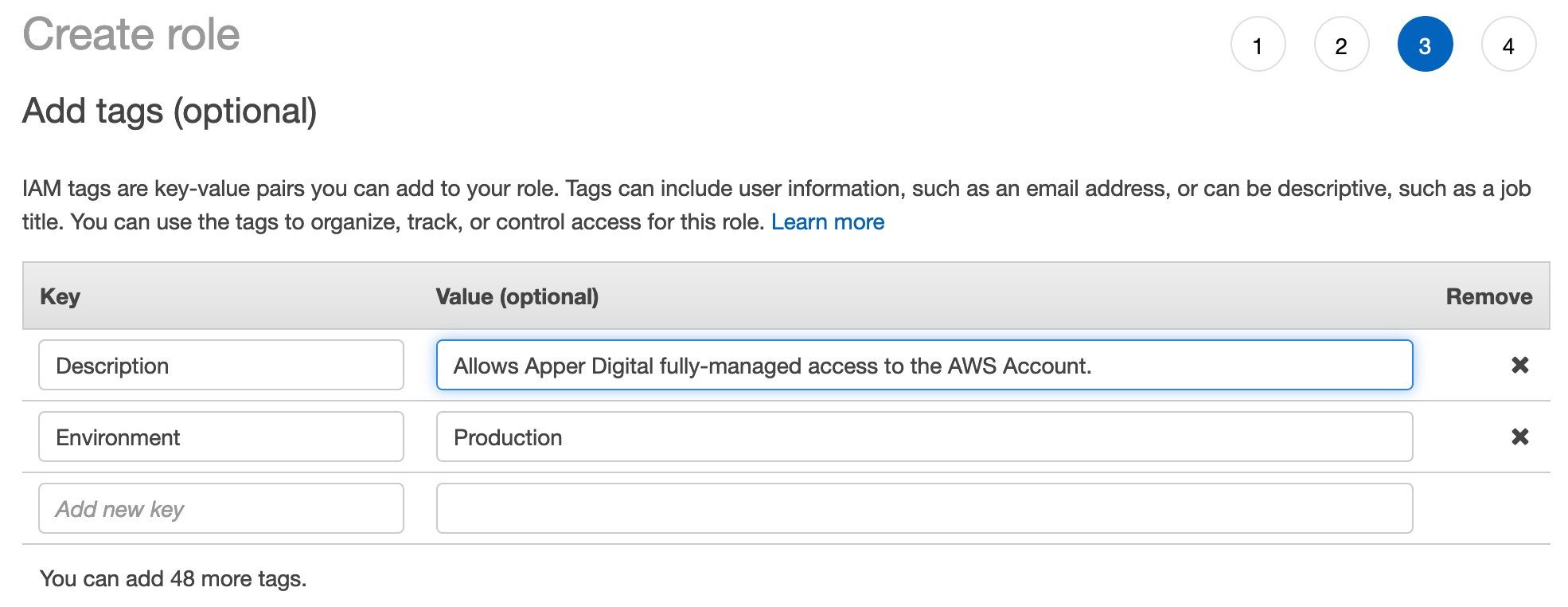
The first step is to create an AWS account alias. Go to the menu, and select My Account to go to IAM.
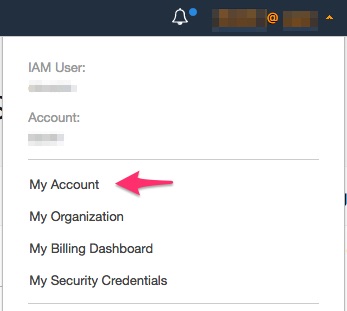
Customize the value of the account alias. Pick an easy to remember account alias that represents your AWS account.
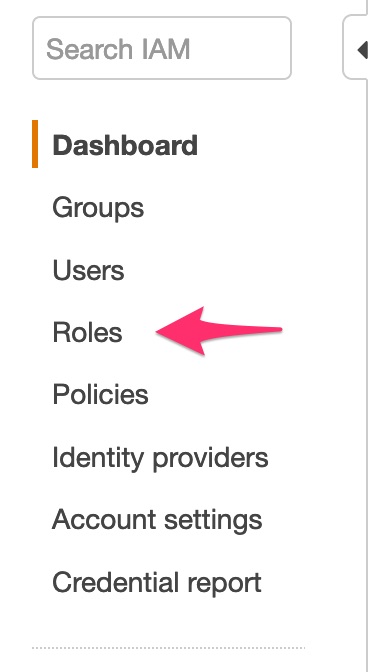
Once the account alias is set up, go to Roles from the menu on the left pane.
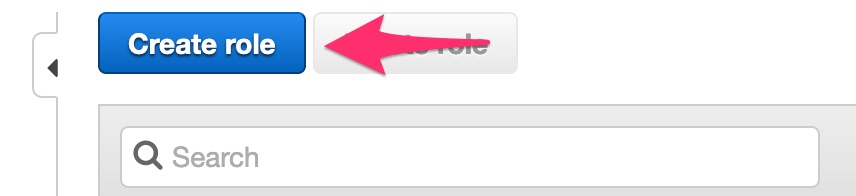
Click “Create role.”
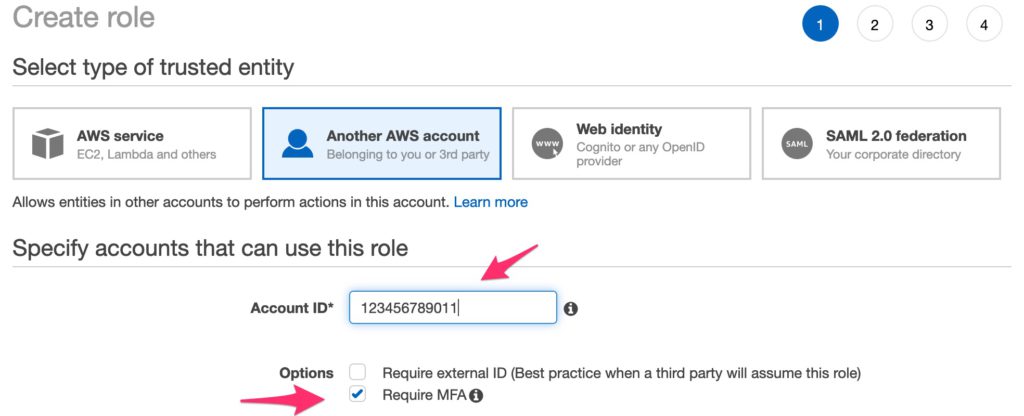
In the Create role screen, select “Another AWS account” for the trusted entity. Input the 3rd party AWS account ID (12-digits). For extra security, tick the “Require MFA.”
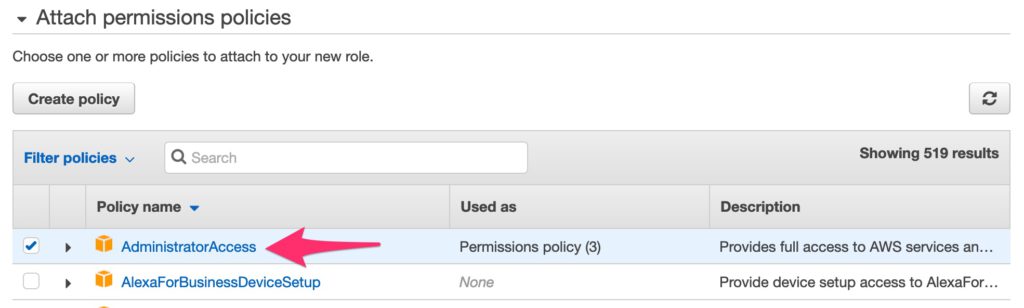
In the next screen, select the permission for the 3rd party. For this guide, Administrator access is given to the 3rd party to perform management and provisioning actions.
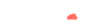
In the tags screen, enter a Description and Environment for easier resource management.
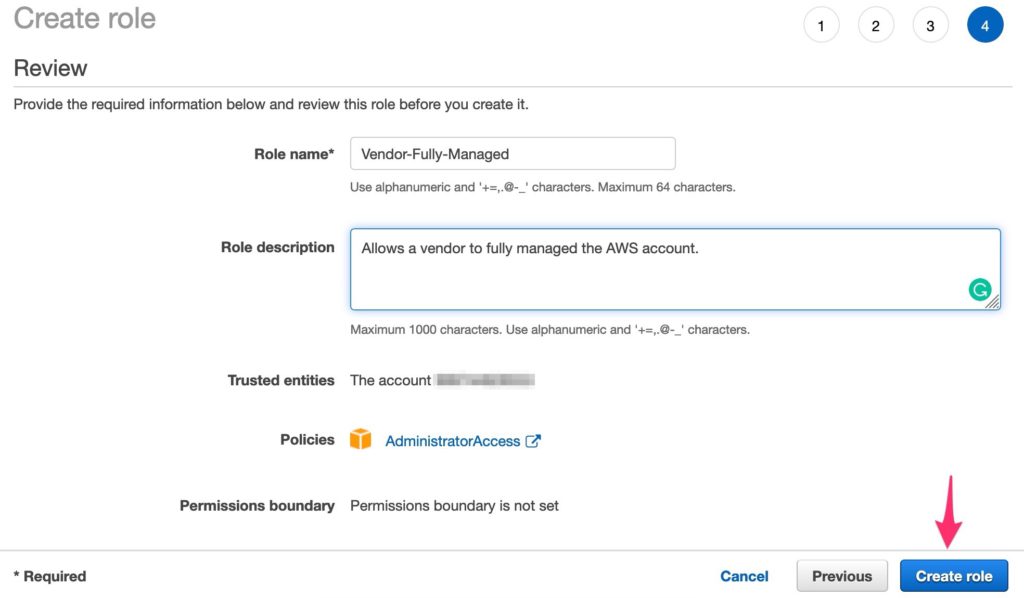
Click the next button and input the Role name and description. Click “Create role.”

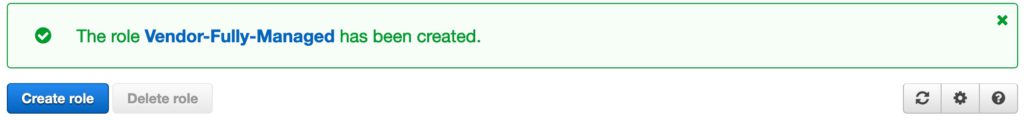
That’s it! The 3rd party can now access your AWS account by assuming that you have created.

Diwa del Mundo
Principal Cloud Architect
Diwa holds eleven AWS certifications (Professional, Specialty, Associate). Aside from his professional interest in AWS, Diwa is also active in the community as an AWS User Group Philippines Cloud Community Leader - Core. He is an experienced IT professional with more than ten years of experience. He is passionate in helping individuals and organizations get into the cloud.